Tag Archives: hacker
Android Diva Series: Insecure Data Storage Part 4

Hello dear friends and welcome back for another Android Diva series blog, today we will resolve Insecure Data Storage Part 4. So first of all, we have to store some value For this exercise, we will use jadx and adb So what we will do is to analyze the… Read more »
Android Diva Series: Insecure Data Storage Part 1

Hello dear friends and welcome back for another Android Diva series blog, today we will resolve Insecure Data Storage Part 1. For this exercise, we will use adb, first at all fill the text fields after that connect adb to the device adb connect ip get a shell adb… Read more »
Android Diva Series: HardCoding Issues Part1
Android Diva Series: Installation and Insecure log exercise

Hello dear friends, today we will start a new series based on Android penetration testing. We will go to analyze the diva application. WHAT IS DIVA? DIVA (Damn insecure and vulnerable App) is an App intentionally designed to be insecure. We are releasing the Android version of Diva. We thought… Read more »
CTF: Android UnCrackable-Level1

Hello, dear friends today I’ll show you how to resolve the CTF Uncrackable – Android Level1. First, we need to install the application in order to understand what it does and how it works adb install UnCrackable-Level1.apk mmm interesting there is a root detection, so now we will use jadx… Read more »
Inject Frida inside an ipa file

Hello dear friends and welcome back for another mobile security blog, today I’ll show you how to inject frida inside an ipa application. So for todo that we need to install some tools: iOS Deploy brew install node npm install -g ios-deploy If you want to know more about this… Read more »
Frida: Demo 1 How to Hack an Android Application

Hello dear friends, and welcome back for another mobile application security blog, today I’ll show you how to bypass a login form with Frida. For this exercise, I did prepare an easy android Application that you can download from this link. After the download run the app on gennymotion emulator…. Read more »
CTF Vulnhub: Hackme 1 Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve hackme: 1machine. Description ‘hackme’ is a beginner difficulty level box. The goal is to gain limited privilege access via web vulnerabilities and subsequently, privilege escalate as root. The lab was created to mimic the real-life environment. ‘hackme’… Read more »
CTF: DC-3 Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve DC-3 machine. Description DC-3 is another purposely built vulnerable lab with the intent of gaining experience in the world of penetration testing. As with the previous DC releases, this one is designed with beginners in mind, although this… Read more »
CTF: LazySysAdmin Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve LazySysAdmin machine. Description Difficulty: Beginner – Intermediate Boot2root created out of frustration from failing my first OSCP exam attempt. Information gathering TCP Scanning Banner Grabbing Nmap scanning Dirb When the samba server is running it’s always a good… Read more »
CTF: bulldog Walkthrough
Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve bulldog machine. Description Bulldog Industries recently had its website defaced and owned by the malicious German Shepherd Hack Team. Could this mean there are more vulnerabilities to exploit? Why don’t you find out? 🙂 This is a standard… Read more »
CTF: SP: eric Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve SP: eric machine. Description Eric is trying to reach out on the Internet, but is he following best practice? Flags – /root/flag.txt – /home/eric/flag.txt Tested with VirtualBox DHCP enabled Difficulty: Beginner Should not be as easy as to… Read more »
CTF: zico2: 1 Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve zico2 machine. Description Zico’s Shop: A Boot2Root Machine intended to simulate a real world cenario Disclaimer: By using this virtual machine, you agree that in no event will I be liable for any loss or damage including… Read more »
CTF: Matrix:1 Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve Matrix machine. Description Matrix is a medium level boot2root challenge. The OVA has been tested on both VMware and Virtual Box. Difficulty: Intermediate Flags: Your Goal is to get root and read /root/flag.txt Networking: DHCP: Enabled IP… Read more »
CTF: FristiLeaks Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve FristiLeaks. Description A small VM made for a Dutch informal hacker meetup called Fristileaks. Meant to be broken in a few hours without requiring debuggers, reverse engineering, etc.. Information gathering TCP Scanning Analyze the web app After… Read more »
CTF: W1R3S Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve W1R3S. Description You have been hired to do a penetration test on the W1R3S.inc individual server and report all findings. They have asked you to gain root access and find the flag (located in /root directory). Difficulty… Read more »
CTF: Unknowndevice64 Walkthrough

Hello dear friends, welcome back for another CTF Walkthrough. Today we will solve Unknowndevice64. Description unknowndevice64 v1.0 is a medium level boot2root challenge. The OVA has been tested on both VMware and Virtual Box. Difficulty: Intermediate Flags: Your Goal is to get root and read /root/flag.txt Information gathering TCP Scanning… Read more »
Utilizzare il modulo shodan di metasploit
Ciao a tutti cari amici di iProg, oggi vorrei parlarvi di un modulo di metasploit ovvero shodan_search, in pratica questo modulo utilizza le api di shodan per permetterci di effettuare ricerche direttamente da metasploit. Per chi non lo sapesse shodan è un motore di ricerca, molto spesso viene anche chiamato… Read more »
Creare un piccolo laboratorio per effettuare pentesting

Uno dei problemi che si incontrano quando uno inizia a cimentarsi nella sicurezza informatica è quello di non sapere dove testare le cose studiate senza far “danni”. Fortunatamente il team di metasploit ha rilasciato una macchina virtuale chiamata ‘Metasploitable’, questa VM può essere utilizzata per effettuare attività di formazione di sicurezza… Read more »
Fingerprinting: Discover script

Ciao a tutti cari amici di iProg, in questo tutorial di oggi voglio mostrarvi un altro tool molto potete ed utile durante la fase di Fingerprinting, il tool si chiama Discover ed è possible scaricarlo dal seguente indirizzo, una volta scaricato spostiamoci all’interno della cartella discover e lanciamo lo script cd discover… Read more »
Sicurezza informatica: Fingerprinting

Ciao a tutti cari amici di iProg , oggi continuiamo a parlare di sicurezza informatica più precisamente discuteremo di fingerprinting o se preferite “raccolte d’informazioni”, se già avete effettuato qualche pentest come potete sapere questa è una delle fasi più importanti. Molte persone che si avvicinano per la prima volta nel campo… Read more »
Come Hackerare un dispositivo Android

Ciao a tutti cari amici di iProg, nel tutorial di oggi voglio mostrarvi come poter hackerare un dispositivo Android attraverso l’ausilio di metasploit. Per chi non lo sapesse metasploit è un framework che consente ai penterster di velocizzare il processo di creazione di un exploit, ovviamente questo è una descrizione abbastanza… Read more »
mitmf Man in the middle
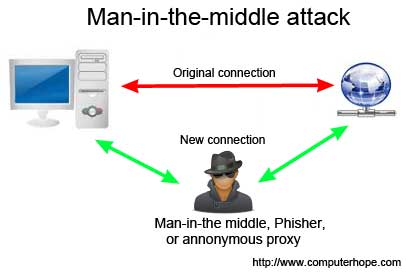
Ciao a tutti cari amici di iProg era da parecchio che non scrivevo un articolo, ma purtroppo sono stato molto occupato in questo periodo. Qualche tempo fa vi accennai in cosa consiste un attacco di tipo man in the middle, oggi vorrei mostrarvi un tool straordinario che si chiama mitmf ed… Read more »